Buy our over-priced crap to help keep things running.




















| File - Download Tor Browser v14.0.7 | ||||||||
| Description | ||||||||
|
A plea... Deanna and I have been running this site since 2008 and lately we're seeing a big increase in users (and cost) but a decline in percentage of users who donate. Our ad-free and junkware-free download site only works if everyone chips in to offset the revenue that ads on other sites bring in. Please donate at the bottom of the page. Every little bit helps. Thank you so much. Sincerely, your Older Geeks: Randy and Deanna Always scroll to the bottom of the page for the main download link. We don't believe in fake/misleading download buttons and tricks. The link is always in the same place. Tor Browser v14.0.7 Protect yourself against tracking, surveillance, and censorship. • Browse Privately. • Explore Freely. • Defend yourself against tracking and surveillance. • Circumvent censorship. 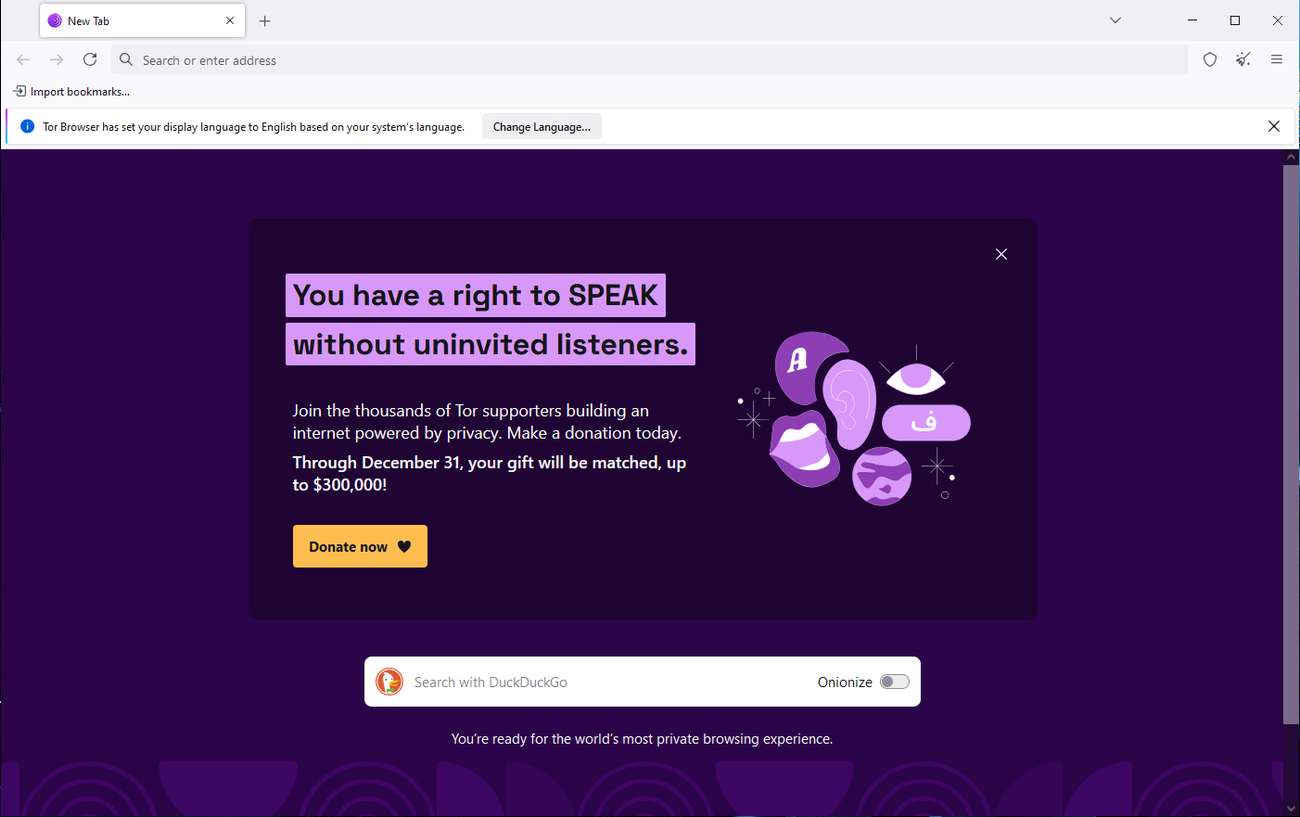 Tor Team mission: To advance human rights and freedoms by creating and deploying free and open source anonymity and privacy technologies, supporting their unrestricted availability and use, and furthering their scientific and popular understanding. BLOCK TRACKERS Tor Browser isolates each website you visit so third-party trackers and ads can't follow you. Any cookies automatically clear when you're done browsing. So will your browsing history. DEFEND AGAINST SURVEILLANCE Tor Browser prevents someone watching your connection from knowing what websites you visit. All anyone monitoring your browsing habits can see is that you're using Tor. RESIST FINGERPRINTING Tor Browser aims to make all users look the same, making it difficult for you to be fingerprinted based on your browser and device information. MULTI-LAYERED ENCRYPTION Your traffic is relayed and encrypted three times as it passes over the Tor network. The network is comprised of thousands of volunteer-run servers known as Tor relays. BROWSE FREELY With Tor Browser, you are free to access sites your home network may have blocked. Changes: Read the latest release announcements 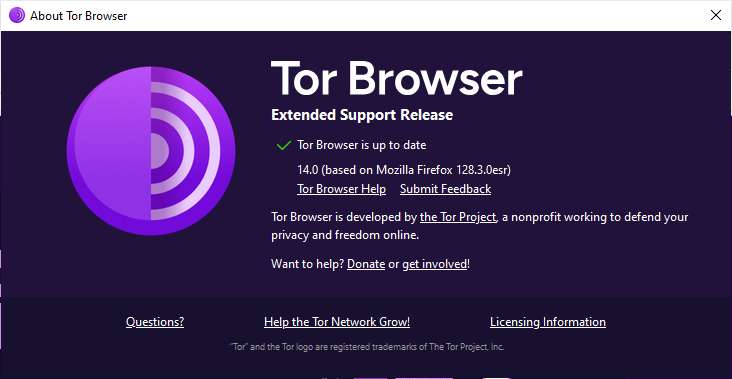 This download is for the Windows 64bit version (very bottom of page). All other download assets are below: Windows: tor-browser-windows-i686-portable-14.0.7.exe (32bit) MacOS: tor-browser-macos-14.0.7.dmg Linux: tor-browser-linux-x86_64-14.0.tar.xz tor-browser-linux-i686-14.0.tar.xz Android: tor-browser-android-aarch64-14.0.7.apk tor-browser-android-armv7-14.0.7.apk tor-browser-android-x86_64-14.0.7.apk tor-browser-android-x86-14.0.7.apk Google Play Store Click here to visit the author's website. Continue below for the main download link. |
||||||||
| Downloads | Views | Developer | Last Update | Version | Size | Type | Rank | |
| 5,965 | 14,055 | The Tor Project <img src="https://www.oldergeeks.com/downloads/gallery/thumbs/TOR1_th.png"border="0"> | Mar 16, 2025 - 12:44 | 14.0.7 | 105.39MB | EXE |  , out of 52 Votes. , out of 52 Votes. |
|
| File Tags | ||||||||
| Tor Browser v14.0.7 | ||||||||
Click to Rate File Share it on Twitter → Tweet
|