|
|

Your download link is at the very bottom of the page... always. |
Processed through Paypal No account required. |
Buy our over-priced crap to help keep things running.










|
|

Your download link is at the very bottom of the page... always. |
Processed through Paypal No account required. |










| Files | ||||
| File Name | Rating | Downloads | ||
| Command No Window v1.0.0.0 Command No Window v1.0.0.0 Run Command Line Scripts Without Displaying a Window. Utility that allows to run command line programs and scripts without displaying the command line, or console window. (This utility by itself will not display any UI if it was run with command line arguments.) Such can be helpful when running commands on schedule without distracting the work of a logged-in user at the time when the schedule is triggered to run. This utility can run Windows executable programs, DOS batch files (text files with .bat or .cmd extensions), as well as PowerShell scripts (text files with .ps1 extension.) If receiving the output from running a command is required, make sure to enable Windows Event Logging via the VerboseLog registry value, described in the included manual. Windows XP/Vista/7/8/10 & Windows Server 2003/R2/2008/R2/2012/R2/2016 Click here to visit the author's website. |
 |
2,798 | May 27, 2021 Dennis Babkin  |
|
| Desktop Icon Spacing v1.0.0.0 Desktop Icon Spacing v1.0.0.0 It allows you to set the space between desktop icons. It treats vertical and horizontal spacing separately. You don’t have to restart the PC to apply changes. Desktop Icon Spacing is part of the system font changer software family. Software startup and recovery options are the same as in other software in the family. Before adjusting the settings, you should close any other windows and save workflow data, as the software restarts the explorer process to apply the settings. It stores current settings. When you start your computer, the previously used settings are applied. You only need to run the software if you want to change current settings. After you run it, the arrangement of icons usually changes. If the explorer process doesn’t restart on your PC, you can start it manually from the “Advanced” menu. If this also fails, use the Ctrl+Alt+Delete keyboard shortcut to restart your computer, or select one of the displayed options. Desktop Icon Spacing is free to use and doesn’t require activation. MD5: 5a5f22d4ddd26807dc0cee4ee1d95487 Click here to visit the author's website. |
 |
2,766 | Apr 24, 2021 Peter Panisz |
|
| ExSleep v1.0.0.0 ExSleep v1.0.0.0 A free, portable app to put your computer asleep by clicking an icon. With filters, it can avoid sleeping computer if there are running programs that shouldn't be interrupted. Avoid sleep by mistake One big problem of Windows build-in sleep button is, it always forces computer to sleep, even when there are tasks that shouldn't be interrupted, e.g. downloading. It is very much possible that you just forgot those tasks, at the time when you decided to put your computer to sleep. ExSleep uses filters to avoid the problem. When you launch ExSleep, it first checks all running programs, and won't sleep the computer if there are programs that match any filter. ExSleep doesn't have GUI, so you need to modify the ExSleep.ini directly if you want to use filters, add one or more filters under section [filters], one filter per line. A filter can be: Full pathname (c:\windows otepad.exe) Filename only (notepad.exe) Filename without extension (notepad) Fullpath or filename with wildcards (*pad.exe) Regular expression (regexp:.*\.+pad.exe) * To use regular expression, keyword regexp: must be in front of a filter. Use desktop shortcut You surely can create a shortcut of ExSleep on desktop, so that you can easily use it by double-clicking. You also can use commmand line parameter -h or -hibernate to hibernate system instead of sleeping. Of course if you want, you can create two shortcuts for both sleep and hibernating. For: Windows 7, 8, 10 Note: This file has a few hits on VirusTotal. These are false positives. The program is safe. Some antivirus engines don't like files that force your computer to go to sleep. Create a shortcut on your desktop Edit the ExSleep.ini to create filters Click here to visit the author's website. |
 |
2,749 | Apr 15, 2021 EaseXP  |
|
| Phoenix Customizer v1.0.0.0 Phoenix Customizer v1.0.0.0 Customize Windows like never before for free. Phoenix Customizer gives you different settings that allow you to customize your Windows 11 or Windows 10 system. You can easily customize Windows folders with different colors and effects, add a custom taskbar that you can change to your liking, have a floating widget with access to your favorite shortcuts and items, or modify the Windows context menu. Windows Folder Customizer Customize your Windows folder icons with ease. It’s simple, select a Windows folder that you would like to change the icon of then click Apply. Phoenix Taskbar Bored or don’t like the Windows Taskbar and want something a little different? Why not try out Phoenix Taskbar as it has many customizable options available, with more to come soon. Phoenix Widget Have you ever wanted a floating icon that you can expand that has all of your favorite shortcuts and items? Well, you can do just that with Phoenix Widget. Phoenix Organizer Add organizers to your Windows desktop and drag your files, folders, shortcuts, and anything else you want onto them, to keep your Windows desktop organized. Customize Windows Add shortcuts to the Windows context menu and have them appear in a way you like. For example, add an item to the desktop context menu, Folder context menu, or even the files context menu. Click here to visit the author's website. |
 |
216 | Dec 03, 2024 ComputerSluggish  |
|
| Run as Service v1.0.0.0 Run as Service v1.0.0.0 RunAsService is a command line tool that allows you to setup a regular console application to run as a service. Below you will find descriptions and examples of how to do this. This tool requires that .NET Framework 2.0 be already installed on your computer. If you do not have .NET Framework 2.0 this tool will display a message and not run. You probably already have the .NET Framework 2.0 but if you don't you can download it here: Microsoft Download Center IMPORTANT: Any services you install using this tool will require that this tool remain on that computer in the same location in order for those services to continue functioning. Therefore before installing any services you should make sure this tool is somewhere where it can remain permanently. If you do end up moving this tool use the 'fixservices' action to fix the existing services. (details on how to use 'fixservices' can be found below) RunAsService Typing just the name of the tool without specifying any parameters. Or specifying incorrect paramters will bring you to the help screen. RunAsService install [Name] [Display Name] PathToExecutable Name The name of the service, if none is specified the name will default to the name of the executable. You might choose to give it a different name than the executable to keep some kind of existing convention, make it friendlier or make it easier to use commands like 'net start' and 'net stop' Display Name ... |
 |
5,255 | Nov 15, 2019 Luis Perez  |
|
| ShadowGuard v1.0.0.0 ShadowGuard v1.0.0.0 ShadowGuard is designed to detect when malware or ransomware is attempting to delete File Shadow Copies and take action. Typically ransomware will attempt to delete Shadow Copies of your files prior to encrypting, so you can’t restore them, but ShadowGuard can step in at this stage to stop it completely. Upon detection ShadowGuard will: Prevent the command from execution (Preserving your Shadow Copies) Terminate the application that initiated the command (This would be the potential ransomware.) ShadowGuard works by attaching itself as a debugger to certain processes, filtering out destructive commands before the process is even created. ShadowGuard can currently attach to: vssadmin.exe wmic.exe powershell.exe ShadowGuard also maintains an allowed programs list which will prevent those programs from being terminated by ShadowGuard. This is extremely useful for some backup applications which may use vssadmin.exe in order to manage volume shadow copies. Compatibility: Windows 10. Although officially unsupported, it will work on older versions of Windows back to Windows XP. How to use it: 1. Download/Install/Run the program. 2. Put a check in the box for each file you wish to guard to enable that feature. Remove the check to disable. 3. Close the program, it does not need to be running to operate. License: ShadowGuard is free for all personal and commercial usage. See included EULA for more details. Click here to visit the author's website. |
 |
2,986 | Feb 17, 2021 d7xtech.com 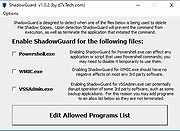 |
|
| Showing rows 1 to 6 of 6 | Showing Page 1 of 1 | 1 |
OlderGeeks.com Copyright (c) 2025