Buy our over-priced crap to help keep things running.




















| Files | ||||
| File Name | Rating | Downloads | ||
| Check Browsers' LNK v2.2.0.34 Check Browsers' LNK v2.2.0.34 Check Browsers' LNK checks usual (*.LNK) and the Internet (*.URL) shortcuts to detect harmful links aimed to show undesirable ads in browsers. Usage: 1) Disable temporarily your antivirus. 2) Run the file. 3) Wait the completing of the work…* After scanning, the folder “LOG” will be opened near the program and the report Check_Browsers_LNK.log that is to be placed in the theme of helping you. Some prefixes description: >>> - shortcuts recommended to be cured. When drag & drop the log to program ClearLNK, they will be cured automatically. - (minus) - shortcuts that will be excluded from the list of ClearLNK program handling. If you need to cure some of them, just copy line to the main window of ClearLNK and press 'Cure'. !!! – files needed special attention The developers: - Pol’shyn Stanislav (Alex Dragokas) - regist Translations maded by: English: Ganna Khatser. French: Fr33tux (fr33tux.org). German: Natalia Ishyna. |
 |
5,457 | Nov 13, 2019 Alex Dragokas  |
|
| Portforward Check v1.1.2 Portforward Check v1.1.2 GUI app for Windows to correctly check if port is open/accessible, separately for TCP and UDP. Use 7-Zip to unzip this file. Click here to visit the author's website. |
 |
1,472 | Sep 13, 2023 setsumi 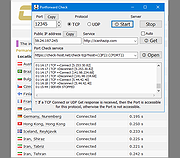 |
|
| Windows 11 Requirements Check Tool v1.4.0 Windows 11 Requirements Check Tool v1.4.0 A free tool to see if your PC meets the requirements to run Windows 11. In addition it checks if your PC can support (gaming) features like AutoHDR and DirectStorage. Runs on Windows 8.1, Windows 10 or Windows 11. Supports 32-bit and 64-bit systems, including Windows on ARM. This tool is a standalone Win32 application written in C++. It does not install anything and spawns no additional processes. Requirement Checks The tool performs the following checks as specified in this document from Microsoft: System Type – Shows whether your PC contains an x86, x64 or ARM-processor. In addition it shows if your operating system is 32-bit or 64-bit. This item turns red if your processor does not support 64-bit instructions and registers, also known as long mode. Windows – Shows the version of Windows you are running. This item checks if your version of Windows can be upgraded to Windows 11. Processor – Shows the processor in your computer. This item checks if your processor has at least 2 cores and runs at 1 GHz or higher. In addition, this item also checks if your processor supports the following features and instructions: PAE (Physical Address Extension) is a processor feature that enables x86 and x86-64 processors to access more than 4 GB of physical memory on capable versions of Windows. NX (No-eXecute) is a processor feature that allows memory pages to be marked as non-executable. The feature enables the processor to help protect against malicious code exploits and is an integral part of hardware-enforced Data Execution Prevention (DEP). If not supported, check your BIOS whether "Data Execution Prevention," "XD," "Execute Disable," or "NX" is disabled. DEP is a Windows feature since 2004 (Windows XP SP2). SSE4.1 (Streaming SIMD Extensions 4.1) ... |
 |
2,360 | Feb 01, 2022 ByteJams.com  |
|
| Showing rows 1 to 3 of 3 | Showing Page 1 of 1 | 1 |
OlderGeeks.com Copyright (c) 2025