Buy our over-priced crap to help keep things running.




















| File - Download EncryptPad v0.4.0.4 for Mac | ||||||||
| Description | ||||||||
|
A plea... Deanna and I have been running this site since 2008 and lately we're seeing a big increase in users (and cost) but a decline in percentage of users who donate. Our ad-free and junkware-free download site only works if everyone chips in to offset the revenue that ads on other sites bring in. Please donate at the bottom of the page. Every little bit helps. Thank you so much. Sincerely, your Older Geeks: Randy and Deanna Always scroll to the bottom of the page for the main download link. We don't believe in fake/misleading download buttons and tricks. The link is always in the same place. EncryptPad v0.4.0.4 for Mac EncryptPad is an application for viewing and editing symmetrically encrypted text. Using a simple and convenient graphical and command line interface, EncryptPad provides a tool for encrypting and decrypting binary files on disk while offering effective measures for protecting information, and it uses the most widely chosen quality file format **OpenPGP** [RFC 4880](https://tools.ietf.org/html/rfc4880). Unlike other OpenPGP software which main purpose is asymmetric encryption, the primary focus of EncryptPad is symmetric encryption. Features Symmetric encryption Passphrase protection Key file protection Combination of passphrase and key file Random key file generator Key repository in a hidden directory in the user's home folder Path to a key file can be stored in an encrypted file. If enabled, you do not need to specify the key file every time you open files. Encryption of binary files (images, videos, archives etc.) Read only mode to prevent accidental file modification UTF8 text encoding Windows/Unix configurable line endings Customisable passphrase generator helps create strong random passphrases. File format compatible with OpenPGP Iterated and salted S2K Passphrases are not kept in the memory for reuse, only S2K results (more ...) Cipher algorithms: CAST5, TripleDES, AES128, AES256 Hash algorithms: SHA-1, SHA-256, SHA-512 Integrity protection: SHA-1 Compression: ZLIB, ZIP Large multi-gigabyte files are supported Why use EncryptPad? Multi-platform codebase: it has been compiled on three popular operating systems and can be adapted to more. Portable: simply copy the executable to a memory stick or a network drive and use on all your computers. Simple to use: EncryptPad is a text editor and an encryption tool for binary files but it saves encrypted, compressed and integrity protected files. Open source with concise codebase: you can read the code or ask somebody you trust to read it for you to ensure that there are no back doors and your information is safe. OpenPGP file format: you can encrypt a file with another tool (gpg for example) implementing the format and open it with EncryptPad and vice versa. Double protection: randomly generated key files in addition to passphrases. When do I need EncryptPad? You have a file containing sensitive information such as account names, passphrases or IDs. It is stored on an unprotected media or you can't control who accesses the file, whether it is located on a computer at work, a laptop while on the move, a memory stick or a cloud drive. You need to send an encrypted file to somebody with whom you prearranged a shared secret (a passphrase or a key file). In this case, you need to exchange the secret personally (not via an accessible Internet protocol) for the protected file to be decrypted by the recipient. You store or receive a file and need to ensure that it has not been tampered with or corrupted during transmission. EncryptPad uses SHA-1 hashing algorithm to verify the data's integrity. You need protection against a brute force attack in case your storage gets in somebody's hands. EncryptPad allows to generate a key and store it separately from encrypted information. The unwanted person would need two secrets to open an encrypted file: the passphrase and the key. Consider this example: you store your encrypted file on a memory stick, and protect it with a passphrase. In addition to that, you protect the file with a file key and store the key on computers where you open the file. If the memory stick is lost, the passphrase is not enough to decrypt your information. The key file is also needed and it is not on the memory stick. When can I not use EncryptPad? You need to send a file to somebody with whom you have not prearranged a shared secret (a passphrase or a key file). In this case, you need asymmetric encryption with public and private keys. Fortunately, there are many convenient tools suitable for the task. You are on public transport or a common area where somebody can see your screen. EncryptPad is not effective on a computer infected with spyware or a virus. Do not use it on a public, shared or compromised computer if you do not trust its safety. IMPORTANT: Before using EncryptPad ensure that it is legal in your country to use encryption ciphers that EncryptPad provides. You may find useful information at cryptolaw.org. IMPORTANT: If you forgot your passphrase or lost a key file, there is nothing that can be done to open your encrypted information. There are no backdoors in the formats that EncryptPad supports. EncryptPad developers take no responsibility for corrupted or invalid files in accordance with the license. File types The format is determined by an extension of a file. Main extensions of encrypted files are GPG and EPD. GPG This file type conforms to OpenPGP format and it is compatible with other OpenPGP tools. Use it if you need to open a file where EncryptPad is not available. The format does not support double protection (key file + passphrase). So you need to choose between key file or passphrase and cannot use both. In addition, it cannot store file key path in the encrypted file. It means that every time you open a file encrypted with a key file, the application will ask you which key file to use. EPD EncryptPad specific format. Other OpenPGP software will not be able to open it unless the file was only protected with a passphrase. If passphrase only protection was used, the file is effectively a GPG file (see GPG section above). However, when a key file protection is involved, it is a GPG file in a WAD container. See the following chapter for details. Feature support Type Feature Supported Key file path\* OpenPGP compatible File format GPG Passphrase yes n/a yes OpenPGP file GPG Key file yes no yes OpenPGP file GPG Key file and passphrase no n/a n/a n/a EPD Passphrase yes n/a yes OpenPGP file EPD Key file yes yes no Nested: WAD/OpenPGP EPD Key file and passphrase yes yes no Nested: OpenPGP/WAD/OpenPGP * Key file location is persisted in the header of an encrypted file so the user does not need to specify it when decrypting. What is an EncryptPad key file? In symmetric encryption the same sequence is used to encrypt and decrypt data. The user or another application usually provides this sequence in the form of an entered passphrase or a file. In addition to entered passphrases, EncryptPad generates files with random sequences called "key files". When the user creates a key file, EncryptPad generates a random sequence of bytes, asks the user for a passphrase, encrypts the generated sequence and saves it to a file. The format of the file is OpenPGP. Other OpenPGP implementations can also create and open EncryptPad key files as below shell commands demonstrate. When EncryptPad generates a new key file, it is roughly equivalent to the following gpg2 command. pwmake 1024 | gpg2 -c --armor --cipher-algo AES256 > ~/.encryptpad/foo.key pwmake generates a random sequence, which gpg2 in-turn encrypts. It will ask for the passphrase to encrypt the sequence. When you use this key to encrypt test3.txt, the equivalent gpg command is below: gpg2 --decrypt ~/.encryptpad/foo.key \ | gpg2 --passphrase-fd 0 --batch -c --cipher-algo AES256 \ -o /tmp/test3.txt.gpg /tmp/test3.txt The first gpg2 process decrypts foo.key and directs it to descriptor 0 of the second process through a pipe. gpg2 reads the sequence from the descriptor with --passphrase-fd 0. When EncryptPad opens the encrypted file protected with foo.key, the equivalent gpg commands are: gpg2 --decrypt ~/.encryptpad/foo.key \ | gpg2 --passphrase-fd 0 --batch --decrypt \ -o /tmp/test4.txt /tmp/test3.txt.gpg As you see, other OpenPGP implementations can also use EncryptPad keys. EPD file format when encrypting with a key There are three different structures a saved file can have depending on protection mode: Passphrase only (passphrase is used to protect a file but no keys are specified). The file is an ordinary OpenPGP file. Key only (passphrase is not set but a key file is used for protection). The file is a WAD file. WAD is a simple format for combining multiple binary files in one. You can open a WAD file in Slade. It contains two files internally: OpenPGP file encrypted with the key __X2_KEY is a plain text file containing the path to the key if "Persistent key location" in the encrypted file is enabled. Otherwise, it has zero length. Protected with passphrase and key. The resulting file is an OpenPGP file containing a WAD file as explained in 2. Use CURL to automatically download keys from a remote storage If CURL URL is specified in Key File Path field in the Set Encryption Key dialogue, EncryptPad will attempt to start a curl process to download the key from a remote host. If you want to use this feature, you need to set the path to the CURL executable in the EncryptPad settings. Consider this use case scenario: you travel with your laptop and open an encrypted file on the laptop. If you protect the file with a passphrase and a key and your laptop is lost or stolen, the perpetrator will be able to make a brute force attack on your file because the key is also stored on the laptop. To avoid this, EncryptPad takes the following steps: Encrypts the plain text file with the key Copies the encrypted file into a WAD file together with the unencrypted HTTPS or SFTP URL to the key file containing authentication parameters. Encrypts the WAD file from point 2 with the passphrase. If this file gets into the hands of a wrongdoer, he or she will need to brute force the passphrase first to be able to obtain the key URL and the authentication parameters. Since a brute force attack takes a lot of time, the user will be able to remove the key or change the authentication so the previous parameters become obsolete. Known weaknesses EncryptPad stores unencrypted text in memory. If a memory dump is automatically taken after a system or application crash or some of the memory is saved to a swap file, the sensitive information will be present on the disk. Sometimes it is possible to configure an operating system not to use a dump and swap files. It is a good practice to close EncryptPad when not in use. Command line interface encryptcli is the executable to encrypt / decrypt files in command line. Run it without arguments to see available parameters. Below is an example of encrypting a file with a key: # generate a new key and protect it with the passphrase "key". # --key-pwd-fd 0 for reading the key passphrase from descriptor 0 echo -n "key" | encryptcli --generate-key --key-pwd-fd 0 my_key.key # encrypt plain_text.txt with my_key.key created above. # The key passphrase is sent through file descriptor 3 cat plain_text.txt | encryptcli -e --key-file my_key.key \ --key-only --key-pwd-fd 3 -o plain_text.txt.gpg 3< <(echo -n "key") Installing EncryptPad Portable executable Portable binaries are available for Windows and macOS. They can be copied on a memory stick or placed on a network share. Changes: Version 0.4.0.4 Portable software should be able to store all its files in a single removable location such as a memory stick. EncryptPad creates its setting file in $HOME/.encryptpad. After this change EncryptPad will check if there is encryptpad_repository directory in the application path and use it for settings and key files. Botan has been updated to version 2.7. Plog has been updated to version 1.1.4. Translation to Lithuanian 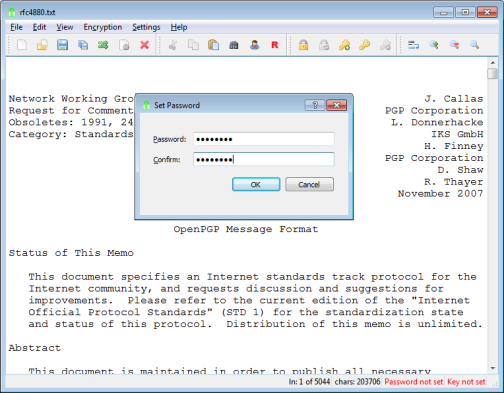 Click here to visit the author's website. Continue below for the main download link. |
||||||||
| Downloads | Views | Developer | Last Update | Version | Size | Type | Rank | |
| 4,976 | 7,496 | Evgeny Pokhilko <img src="https://www.oldergeeks.com/downloads/gallery/thumbs/EncryptPad1_th.png"border="0"> | Nov 19, 2019 - 12:34 | 0.4.0.4 | 31.83MB | DMG |  , out of 65 Votes. , out of 65 Votes. |
|
| File Tags | ||||||||
| EncryptPad v0.4.0.4 for Mac | ||||||||
Click to Rate File Share it on Twitter → Tweet
|