Buy our over-priced crap to help keep things running.




















| Files | ||||
| File Name | Rating | Downloads | ||
| Media_Repair v1.0.0.122 Media_Repair v1.0.0.122 Media_Repair will attempt to repair files encrypted by STOP/DJVU ransomware variants by making the non-encrypted part of the file playable again. Media_Repair does not decrypt files. Media_Repair currently supports following file types: WAV* MP3 Mp4* M4V* MOV* 3GP* * reference file required For most file types Media_Repair requires a reference file: This is an INTACT file created on the same device or using the same software. Ideally this reference file matches the settings that were used to create the ‘patient’ file as closely as possible. Media_Repair can not repair all files! Video that was optimized for internet streaming (fast start) can not be repaired at this time! "Due to limited testing (I have only so much STOP/DJVU affected files), current version should be considered beta!" - Joep van Steen Using Media_Repair –Use drop down box to select a file type. Now browse to folder containing your STOP/DJVU encrypted or the reference file. You can either use a patient file or reference file to test if this particular video type can be repaired by Media_Repair or not. – Click to verify selected video file is candidate for repair. You can either use the reference file or a corrupt file. If Media_Repair reports it can try repairing the file it is not a guarantee the file will actually be repaired. If it can be repaired depends in several factors such as the reference file being a good match and the size of the patient file. If it tells you it can not repair the file though it’s pretty much a guarantee the repair will fail. – Click to make the currently selected file, reference file that will be used to repair affected file(s). Once you have confirmed your video files are candidates ... |
 |
3,496 | Jun 25, 2020 Joep van Steen  |
|
| RansomNoteCleaner v0.9.4.1 RansomNoteCleaner v0.9.4.1 RansomNoteCleaner (beta) is a program I have created to help remove pesky ransom notes left behind by known ransomware variants. This program is powered by my service ID Ransomware, and thus is always updated with definitions on the latest known ransomwares and their ransom notes. This also allows it to be flexible in detecting the ransom notes, as it uses the exact same data ID Ransomware uses for identifying variants. When RansomNoteCleaner is first launched, it will contact the website, and pull down the latest information on known ransom notes; this is the only network activity done with the program, and no information about your system is uploaded or stored at all. If you have a network issue with reaching the website, the "Refresh Network" button is available to try again. Clicking the "Select Ransomware(s)" button allows for selecting the exact variant(s) to clean ransom notes from. This is recommended if you have already identified the ransomware, as it will take much less time to search for the notes. Once the ransomware variant(s) have been confirmed, you may press the "Search for Ransom Notes" button to select a directory (or whole drive), and start the search for known ransom notes. Once the scan has completed, the "Clean!" button will be available. A final window will display all found ransom notes before continuing with deletion. I highly recommend double-checking the file list before confirming the deletion. I am not responsible for loss of data if you confirm this step. A full log of deleted ransom notes will be saved to a file "RansomNoteCleaner.log" in the same directory RansomNoteCleaner is run from. Please note that this program does not decrypt data. It is simply a tool for removing the pesky ransom notes that are littered on the system after a ransomware attack. Please also ... |
 |
5,217 | Nov 13, 2019 Demonslay335  |
|
| ShadowGuard v1.0.0.0 ShadowGuard v1.0.0.0 ShadowGuard is designed to detect when malware or ransomware is attempting to delete File Shadow Copies and take action. Typically ransomware will attempt to delete Shadow Copies of your files prior to encrypting, so you can’t restore them, but ShadowGuard can step in at this stage to stop it completely. Upon detection ShadowGuard will: Prevent the command from execution (Preserving your Shadow Copies) Terminate the application that initiated the command (This would be the potential ransomware.) ShadowGuard works by attaching itself as a debugger to certain processes, filtering out destructive commands before the process is even created. ShadowGuard can currently attach to: vssadmin.exe wmic.exe powershell.exe ShadowGuard also maintains an allowed programs list which will prevent those programs from being terminated by ShadowGuard. This is extremely useful for some backup applications which may use vssadmin.exe in order to manage volume shadow copies. Compatibility: Windows 10. Although officially unsupported, it will work on older versions of Windows back to Windows XP. How to use it: 1. Download/Install/Run the program. 2. Put a check in the box for each file you wish to guard to enable that feature. Remove the check to disable. 3. Close the program, it does not need to be running to operate. License: ShadowGuard is free for all personal and commercial usage. See included EULA for more details. Click here to visit the author's website. |
 |
2,983 | Feb 17, 2021 d7xtech.com 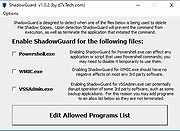 |
|
| WannaSmile 0.1 WannaSmile 0.1 WannaCry Ransomware is spreading like wild fire. It uses vulnerability in Microsoft's SMB ( which is turned on by default ). On 13th may 2017 , security researcher going with the handle @malwaretech and Darien Huss found a 'kill-switch' which paused the ransomware. Basically the ransomware opens a unregistered domain and if fail to open then the system is infected. So @malwaretech registered the domain which stopped the ransomware. Soon Cyber criminals around the world DDOSed it to take it down so that the ransomware can continue affecting. Also the 'kill-switch' won't work if : System is not connected to internet If the 'kill-switch' domain is down If it is blocked by the isp or firewall The solution WannaSmile is a simple program which can solve the problem It can do the following : It will disable SMB in your system ( which is enabled by default ) ( OnlineFix ) It will edit your host file and add google's IP to the 'kill-switch' ( which means even if the site goes down you wont be affected ) ( OfflineFix ) It will create a lightweight local web server and add localhost to 'Kill-switch' Tip Use the OnlineFix if you are always connected to the internet Use the OfflineFix if you are not connected to the internet. How to run You directly run the .exe file and it will do the magic. ( Right-click on file and Run as Administrator ). |
 |
5,289 | Nov 13, 2019 Indrajeet Bhuyan  |
|
| Showing rows 1 to 4 of 4 | Showing Page 1 of 1 | 1 |
OlderGeeks.com Copyright (c) 2025