|
|

Your download link is at the very bottom of the page... always. |
Processed through Paypal No account required. |
Buy our over-priced crap to help keep things running.










|
|

Your download link is at the very bottom of the page... always. |
Processed through Paypal No account required. |










| Files | ||||
| File Name | Rating | Downloads | ||
| 29 Avast Ransomware Decryption Tools 29 Avast Ransomware Decryption Tools Avast has created 29 different tools to decrypt your files encrypted by the following ransomware variants. This is a zip file containing all 29 of them. AES_NI Alcatraz Locker Apocalypse AtomSilo Babuk BadBlock Bart BigBobRoss BTCWare Crypt888 CryptoMix (Offline) CrySiS EncrypTile FindZip Fonix GandCrab Globe HiddenTear Jigsaw LambdaLocker Legion LockFile NoobCrypt Stampado SZFLocker TeslaCrypt Troldesh / Shade XData Click here to visit the author's website. |
 |
4,422 | Oct 28, 2021 Avast Software s.r.o.  |
|
| 80 Emsisoft Ransomware Decryption Tools v1.0 80 Emsisoft Ransomware Decryption Tools v1.0 Unlock your files without paying the ransom This is a compilation of all 80 of Emsisoft's free ransomware decryption tools compiled by OlderGeeks.com. Please note: Due to the nature of decryption tools sometimes carrying ransomware samples to do their work, some antivirus programs may detect viruses in these tools. It is recommended that you disable your antivirus software to use these tools. You may also have to disable your antivirus to unzip the file without any of the tools being deleted. The following tools are included in this zip file: Emsisoft Decryptor for Ragnarok Emsisoft Decryptor for SynAck Emsisoft Decryptor for Ziggy Emsisoft Decryptor for Cyborg Emsisoft Decryptor for Crypt32 Emsisoft Decryptor for CheckMail7 Emsisoft Decryptor for SpartCrypt Emsisoft Decryptor for Zorab Emsisoft Decryptor for RedRum Emsisoft Decryptor for JavaLocker Emsisoft Decryptor for KokoKrypt Emsisoft Decryptor for Ransomwared Emsisoft Decryptor for ChernoLocker Emsisoft Decryptor for TurkStatik Emsisoft Decryptor for Hakbit Emsisoft Decryptor for Jigsaw Emsisoft Decryptor for Paradise Emsisoft Decryptor for STOP Puma Emsisoft Decryptor for STOP Djvu Emsisoft Decryptor for Muhstik Emsisoft Decryptor for HildaCrypt Emsisoft Decryptor for GalactiCrypter Emsisoft Decryptor for Avest Emsisoft Decryptor for WannaCryFake Emsisoft Decryptor for Syrk Emsisoft Decryptor for JSWorm 4.0 Emsisoft Decryptor for LooCipher Emsisoft Decryptor for ZeroFucks Emsisoft Decryptor for Ims00rry Emsisoft Decryptor for GetCrypt Emsisoft Decryptor for JSWorm 2.0 Emsisoft Decryptor for MegaLocker Emsisoft Decryptor for ZQ Emsisoft Decryptor for CryptoPokemon Emsisoft Decryptor for Planetary Emsisoft Decryptor for Aurora Emsisoft Decryptor for HKCrypt Emsisoft Decryptor for PewCrypt Emsisoft Decryptor for BigBobRoss Emsisoft Decryptor for NemucodAES Emsisoft Decryptor for Amnesia2 Emsisoft Decryptor for Amnesia Emsisoft Decryptor for Cry128 Emsisoft Decryptor for Cry9 Emsisoft Decryptor for Damage Emsisoft Decryptor for CryptON Emsisoft Decryptor for MRCR Emsisoft Decryptor for Marlboro Emsisoft Decryptor for Globe3 Emsisoft Decryptor for OpenToYou Emsisoft Decryptor for GlobeImposter Emsisoft Decryptor for NMoreira Emsisoft Decryptor for OzozaLocker Emsisoft Decryptor for Globe2 Emsisoft Decryptor for Globe Emsisoft Decryptor for Al-Namrood Emsisoft Decryptor for FenixLocker Emsisoft Decryptor for Fabiansomware Emsisoft Decryptor for Philadelphia Emsisoft Decryptor for Stampado Emsisoft Decryptor for ApocalypseVM Emsisoft Decryptor for Apocalypse Emsisoft Decryptor for BadBlock Emsisoft Decryptor for Xorist Emsisoft Decryptor for 777 Emsisoft Decryptor for AutoLocky Emsisoft Decryptor for Nemucod Emsisoft Decryptor ... |
 |
2,724 | Oct 16, 2021 Emsisoft Ltd  |
|
| Bitdefender Ransomware Recognition Tool v1.0.0.2 Bitdefender Ransomware Recognition Tool v1.0.0.2 A tool to help ransomware victims find which family and sub-version of ransomware has encrypted their data and then get the appropriate decryption tool, if it exists. Ransomware has grabbed the headlines ever since 2014. While most ransomware attacks can’t be defeated, Bitdefender constantly creates and updates ransomware decryption tools for families that have either vulnerable encryption algorithms or for which a master decryption key has been leaked. This tool analyzes both the ransom note and the encrypted file samples to identify the strain of ransomware and suggest a decryption tool for the identified family, if such a tool is available. Step 1 Download the BRR tool and save it somewhere on your computer. The latest version is always available here. This tool requires an active internet connection. Step 2 Run the BDRansomRecognitionTool.exe and allow it to execute if prompted by an UAC alert. Step 3 Read and agree to the End User License Agreement Step 4 The application has two fields to fill in: Choose the path to the ransom note file or the path to a folder containing encrypted files. You can choose either option, but the tool needs at least one of the pieces of information to detect which strain of ransomware has encrypted your information. If none of the fields are filled in, you cannot proceed any further Step 5 Press Scan. The application gives a warning if the ransom-note path is not filled in, as the detection accuracy is slightly lower in this case. The content of the ransom note is submitted for analysis to Bitdefender cloud. If the user provides any encrypted file, NO file content will be submitted to our cloud, as the tool only analyzes the filename and its extension. If the ransomware family cannot be identified, the user is informed about this. In some cases, multiple families of ransomware display similar features. ... |
 |
5,433 | Nov 13, 2019 BitDefender Labs 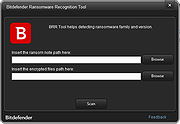 |
|
| Showing rows 1 to 3 of 3 | Showing Page 1 of 1 | 1 |
OlderGeeks.com Copyright (c) 2025