Buy our over-priced crap to help keep things running.




















| File - Download RDP-Parser v1.1 | ||||||||
| Description | ||||||||
|
A plea... Deanna and I have been running this site since 2008 and lately we're seeing a big increase in users (and cost) but a decline in percentage of users who donate. Our ad-free and junkware-free download site only works if everyone chips in to offset the revenue that ads on other sites bring in. Please donate at the bottom of the page. Every little bit helps. Thank you so much. Sincerely, your Older Geeks: Randy and Deanna Always scroll to the bottom of the page for the main download link. We don't believe in fake/misleading download buttons and tricks. The link is always in the same place. RDP-Parser v1.1 RDP-Parser extracts RDP activities from Microsoft Windows Event Logs. This tool has been designed for any investigation involving exploitation of RDP service. It supports Evt and Evtx formats. How it works This is a command line tool and there is no installer. You should unzip and copy the program where you want to use it. Open a command line in the directory where the program is. You can print help message using "RDP-Parser --h": 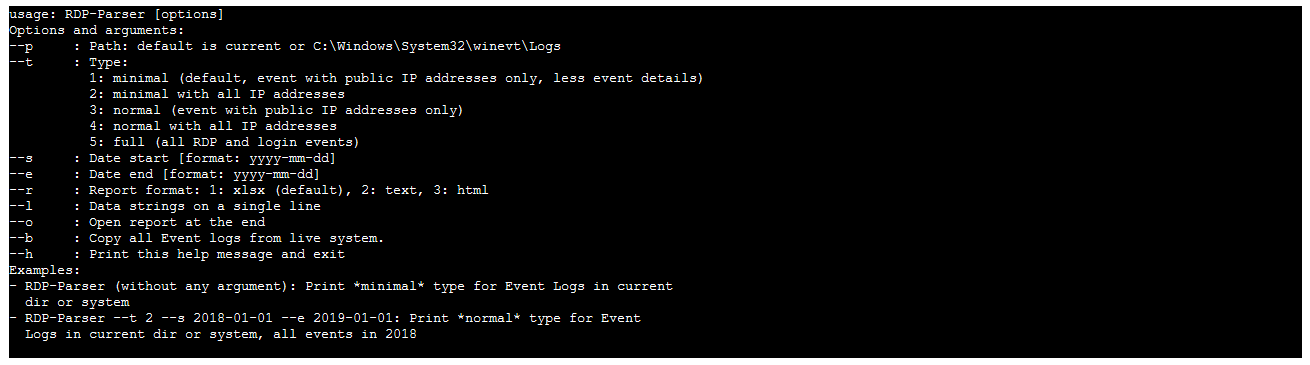 More details about options: --p: By default, RDP-Parser will check in the current directory, so you can copy the program in the same folder as the Event Logs you want to parse. If there is no given path and current directory doesn't contain Event Logs, RDP-Parser will copy the live system Event Logs in the current directory. This command require admin priviledge and it doesn't work for old format logs. --t: There are three types of report: 1: minimal: This is the default type. The report will contain following columns: TimeGenerated, Source, EventID and Details. Only events with public IP addresses will be extracted and all details will be removed except IP address. 2: minimal with all IP addresses: Same as type 1, but it also includes private IP addresses. 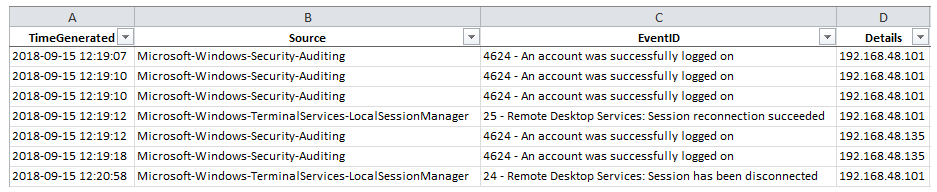 3: normal: The report will contain all columns and all details. Columns are: TimeGenerated, Timewritten, Computer, Source, RecordNumber, Category, EventID, EventType and Details. Only events with public IP addresses will be extracted but all details will be included. 4: normal with all IP addresses: Same as type 3, but it also includes private IP addresses. 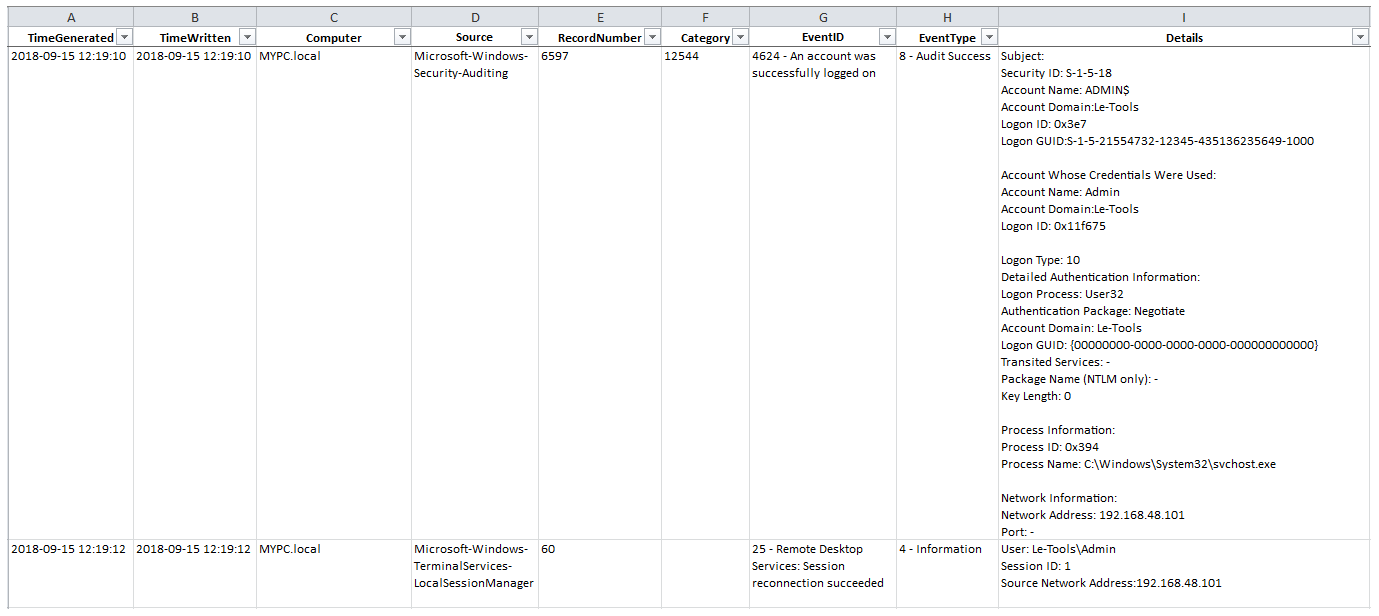 5: full: All events related to RDP or login activities will be included. Included events IDs are: New format (evtx): From Microsoft-Windows-TerminalServices-LocalSessionManager%4Operational.evtx, event ids 21 to 25, 39 and 40; From Microsoft-Windows-TerminalServices-RemoteConnectionManager%4Operational.evtx, event ids 261 and 1149; From Microsoft-Windows-RemoteDesktopServices-RdpCoreTS%4Operational.evtx, event ids 131 and 140; From Security.evtx, event ids 4624, 4625, 4634, 4647, 4778 and 4779; From System.evtx, event ids 56. Old format (security.evt or SecEvent.Evt): Event ids 528 to 540, 552, 682 and 683. Also, all events that contain IP addresses involved with RDP activities will be included. Some events may be not extracted (See known problems about this). --l: With this option, all strings in Details column are on a single line. --b: This is the backup function. It copies all Event logs from live system. All other options will be ignored. This command require admin priviledge and it doesn't work for old format logs. In the command line interface, RDP-Parser provides some important informations about logs as the date and time of the first entry, the last entry and the total number of entries. 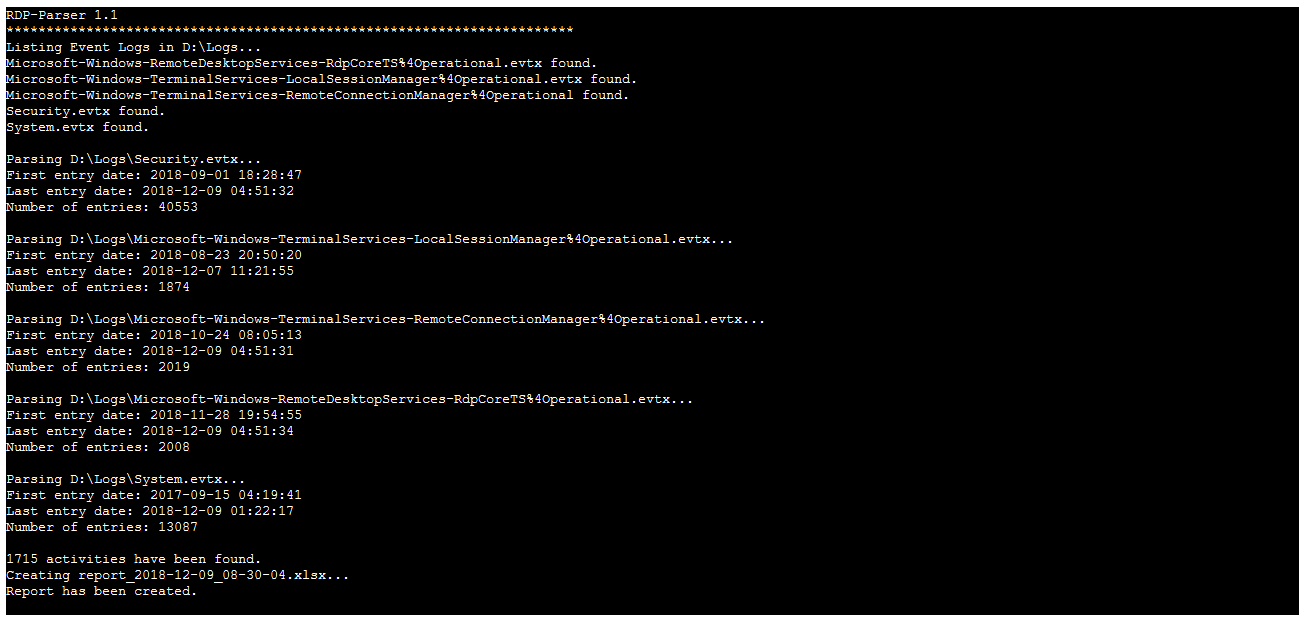 What do you need Windows XP SP2 or newer Changes: 1.1 2018-12-09 New: Extraction of Event IDs 131 and 140 from Microsoft-Windows-RemoteDesktopServices-RdpCoreTS%4Operational.evtx Fixed: Details were not correctly extracted for event 56 and 1149 with types 2, 4 or 5. Known Problems For old format (evt), parsing string for event id 528 (and probably the whole range 528 to 540) is buggy, so you won't get all events, because strings are not correctly parsed. Click here to visit the author's website. Continue below for the main download link. |
||||||||
| Downloads | Views | Developer | Last Update | Version | Size | Type | Rank | |
| 4,734 | 6,981 | Alain Rioux <img src="https://www.oldergeeks.com/downloads/gallery/thumbs/RDPParser1_th.png"border="0"> | Feb 27, 2019 - 01:46 | 1.1 | 2.87MB | ZIP |  , out of 62 Votes. , out of 62 Votes. |
|
| File Tags | ||||||||
| RDP-Parser v1.1 | ||||||||
Click to Rate File Share it on Twitter → Tweet
|